FortiGuard Labs shows in the latest report how cybercriminals are exploiting the global pandemic on a large scale
Fortinet® (NASDAQ: FTNT), a leading global provider of comprehensive, integrated and automated cyber security solutions, has released its latest security report for the first half of 2020.
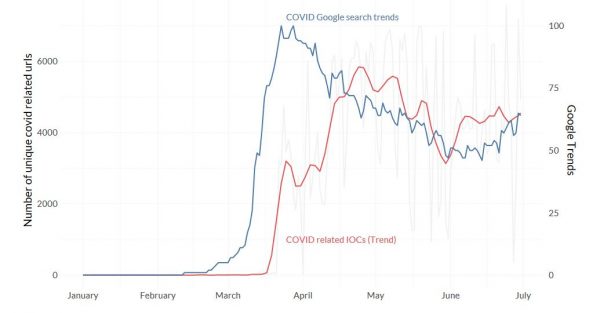
This shows the dramatic extent to which both cybercriminals and nation-state actors used a global pandemic to launch a multitude of cyber attacks around the world. The adaptability of the opponents made waves of attacks possible, which were aimed at the fear and insecurity of current events. In addition, the suddenly large number of remote workers outside the corporate network was a major factor that rapidly expanded the digital attack surface overnight
"The first six months of 2020 witnessed an unprecedented cyber threat landscape Adversaries [...] quickly shift their strategies to maximize the current events centered around the COVID-19 pandemic across the globe [taking] into account the network perimeter extending into the home".
Derek Manky, Chief, Security Insights & Global Threat Alliances, FortiGuard Labs
The main findings
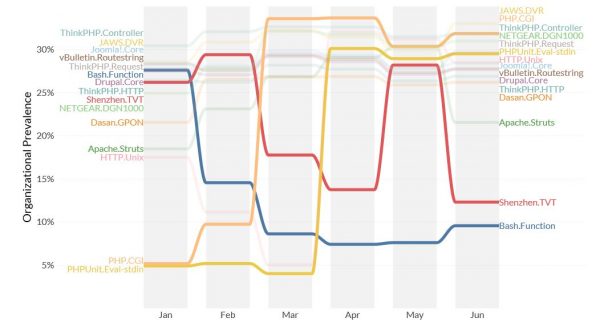
Although many current threat trends are pandemic related, some threats still had their own drivers. For example, ransomware and attacks on Internet of Things (IoT) devices and operational technology (OT) are not decreasing, but are becoming more targeted and sophisticated.
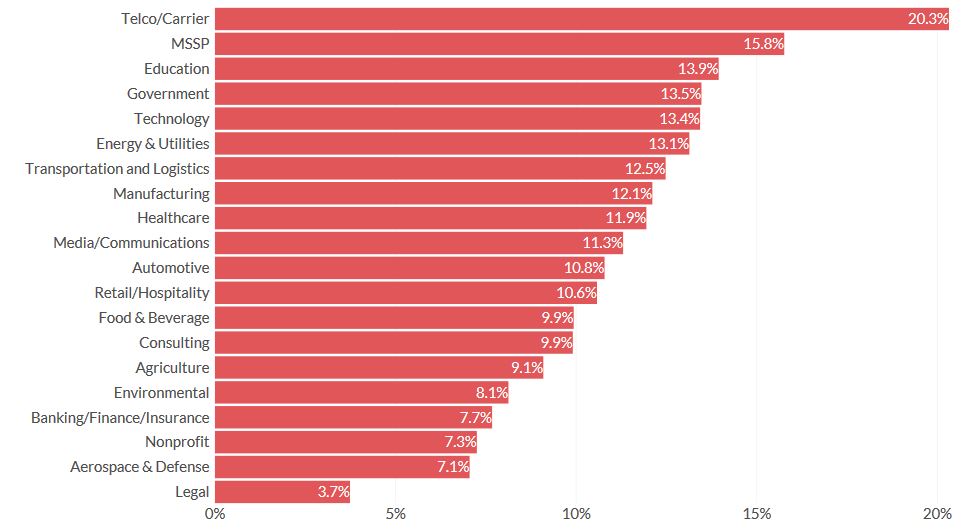
At the global level, most threats are global and cross-sectoral, although there are regional or vertical differences. Similar to the COVID 19 pandemic, a particular threat could occur in one area but then spread globally, meaning that most organisations could be exposed to the threat. There are regional differences in infection rates based on factors such as policies, practices, or responses.
What does this mean for CISOs now?
CISOs should use the information provided in this report to assess and update current security measures to ensure that these attack methods and strategies are adequately protected.
The first step is to re-visit remote workers to ensure that appropriate security measures are in place to protect data, applications and resources used at remote locations and to ensure that they do not become a conduit for malware to find its way into the corporate network. This begins with ensuring adequate security on end-user devices, particularly protecting browser activity as Web-based malware delivered through phishing campaigns and other scams surpassed the more traditional email delivery vector in the first half of 2020.
Endpoint devices should not be protected with traditional anti-virus (AV) and endpoint protection alone. New endpoint detection and recovery (EDR) solutions such as FortiEDR can not only identify sophisticated attacks, but also prevent unknown applications such as malware from running until they have been analyzed.
Companies should already have a robust ransomware strategy. This should include the ability to remove malicious content in an email using tools for disabling and restoring content. Networks must be segmented as part of a ZTNA strategy to limit the resources that can be affected. Complete backups must be stored offline and off-network to ensure fast recovery. And data within the network must be encrypted so that it cannot be used or disclosed by cybercriminals. This must be coupled with a complete response strategy that is applied regularly to avoid downtime.
Ensure that all VPN traffic is scanned - With increasing attacks on home routers and associated devices such as DVRs, it is important that VPN connections include full scanning for malware originating from remote workers' home networks. This requires firewalls that can manage not only a dramatically increased volume of VPN traffic, but also the heavy processing load required to check encrypted traffic.
Increased attacks on OT environments require security that limits the resources that users, devices, applications and workflows can access. Fortinet's complete Zero-Trust Network Access Solution (ZTNA) combines access control and network security solutions to secure OT environments and systems such as SCADA and ICS systems with networking features such as access points and network segmentation. This ensures that malware, even if it manages to bypass edge security strategies, remains confined to a tiny segment of the OT network.
Further Information
ABAX is available to you as a Fortinet partner with our experts on all questions concerning Fortinet solutions would be very happy to help you.